Research Groups
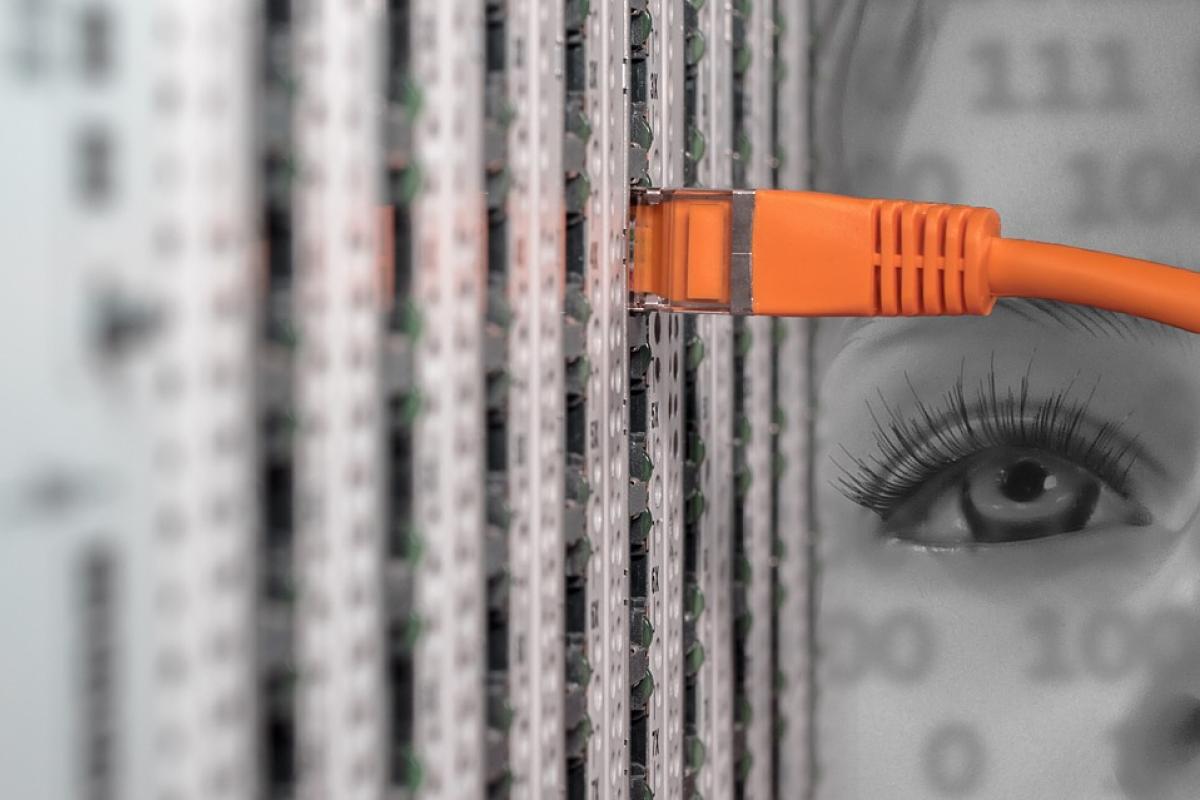
Faculty: Eric Keller and Eric Wustrow
We focus on building (and attacking) practical, reliable, and widely-used networked systems.
Our group builds and studies tools, techniques, and abstractions that help solve these and other real-world problems in network systems and security. Our work spans a broad range of topics, from the security of physical keys to building robust distributed systems using software-defined networks and other virtualization technologies. We have helped design systems that can leverage emerging architecture trends such as SoC (System-on-Chip) FPGA integration in mobile environments, as well as developed new protocols and tools that enable users to circumvent their government’s Internet censorship.
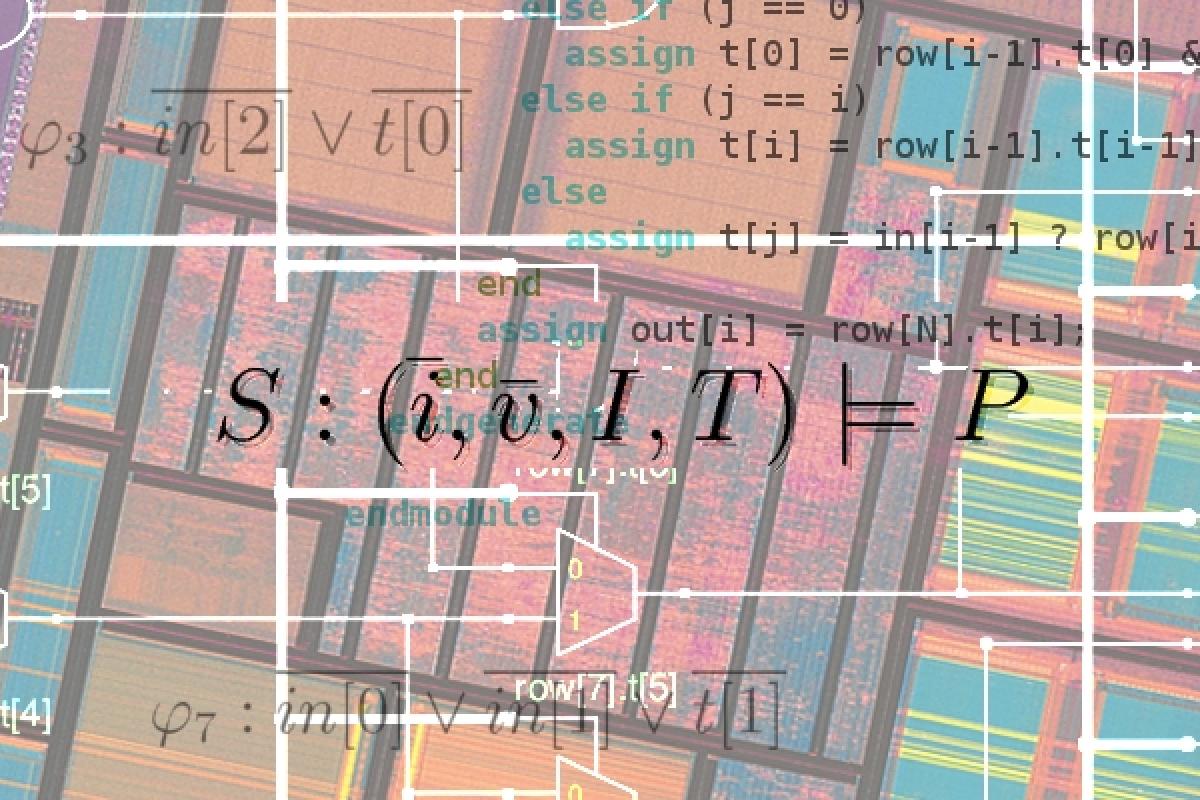
Faculty: Fabio Somenzi and Chris Myers
Our work focuses on improving the productivity of programmers and system designers by developing methods and tools that make it easier to design and verify reliable software and hardware.
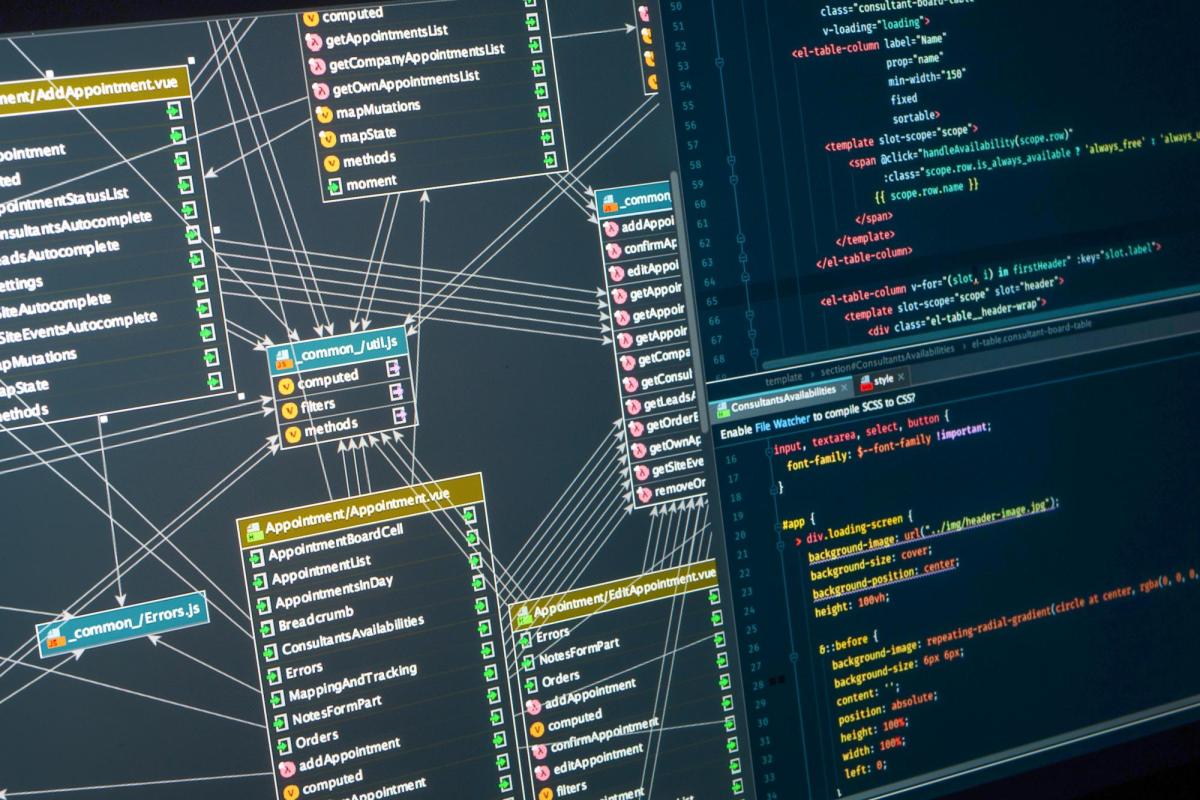
Faculty: Tamara Lehman and Joe Izraelevitz
Our work focuses on developing efficient and secure systems from the hardware up. We work on software and hardware co-design challenges introduced by future technology trends and requirements.